Solutions
Law firms
Tax, audit & accounting firms
Success stories
-
A true competitive advantage
Law firm Zarwin Baum’s embrace of generative AI as the natural next step in the evolution of legal work and their adoption of CoCounsel Legal has helped them achieve remarkable efficiency gains and improved client relationships.
-
Workflow transformation drives impact
Brinks, a global leader in secure logistics and security solutions, used CoCounsel to reimagine what was possible with AI tools, turning legal challenges into a competitive advantage.
-
The forefront of audit tech
A better auditing workflow solution was the answer to multiple challenges faced by The Mercadien Group. Find out how they achieved greater efficiency by embracing Cloud Audit Suite.
Products
Legal
Trade & supply
Tax, audit & accounting
- 1040SCAN
- Audit Intelligence Analyze
- CoCounsel Audit
- CoCounsel Tax
- Ready to Advise
- Ready to Review
- View all
Corporate tax
Recommended products
-
CoCounsel Legal
Transform your work with the only AI legal solution uniting research, drafting, and document analysis in a single experience. Designed by legal experts and built on trusted content and advanced AI, CoCounsel Legal accelerates multistep work so you can better serve your clients and grow your business.
-
CoCounsel Tax
Transform your tax practice with CoCounsel Tax, an AI-powered assistant that combines trustworthy answers, automation, and firm knowledge into one seamless platform. Enhance efficiency, reduce risk, and improve client confidence with CoCounsel Tax.
-
CLEAR Investigate
Intelligently surface critical connections and insights in actionable format through AI-driven research workflows seamlessly integrated with the trusted and transparent CLEAR platform. Accelerate investigations and empower your team to make strategic decisions with confidence.
Purchase
Buy solutions
Resources
Insights
Events
Product training
Product communities
Developers
Highlights
-
2026 SKILLS showcase
Join weekly sessions to experience in-depth demonstrations of the leading legal AI products while connecting with strategic law firm leaders in knowledge management, innovation, and AI.
-
Ghosts on the ledger
Payroll fraud is a major compliance risk. Learn how payroll analytics and AI-powered tools can help exorcise phantom employees and employers.
-
Future of professionals report 2025
The Thomson Reuters Future of Professionals Report 2025 reveals how AI continues to shape professional work — and what it takes to get ahead. This year’s report shows that increased efficiency, productivity, and cost savings top the list of benefits professionals attribute to AI, making it indispensable for organizations facing rapid change.
Contract Express - SSO with Microsoft Entra ID
- API: This Contract Express API application is responsible for core (aka API) functionality; it is usually deployed as a virtual application "/rest".
- UI: This Contract Express UI application is responsible for UI elements; it is usually is deployed as a virtual application "/app".
- ID: This Contract Express Identity Server application is responsible for authentication; it is usually deployed as a virtual application "/id".
- Search: This Contract Express Search application is responsible for the Search feature within UI; it is usually deployed as a virtual application "/search".
Azure – Register a Client Application for Microsoft Graph API
- Navigate to theMicrosoft Azure Portal(https://portal.azure.com/).
- Loginusing your work or school account.
- Navigate toApp Registrationsblade.
- ClickNew registration, and:
- Specify aNamefor the app(for example, Contract Express SSO with Microsoft Entra ID)
- Select the appropriate option from theSupported account types(we strongly recommendunless another option is required)Accounts in this organizational decretory only
- In the Redirect URI section, select theWeboption from the dropdown and enter the Contract Express Identity Server signin-azuread endpoint to%The_ID_URL%/core/signin-azuread(for example, https://contoso.contractexpress.com/id/core/signin-azuread)
- ClickRegister
- You will beredirectedto the created application:
- Take a note ofApplication (client) IDas this is the value ofMSGraphClientId
- Take a note ofDirectory (tenant) IDas this is the value ofMSGraphTenant
- SelectCertificates & secretsblade within just created application.
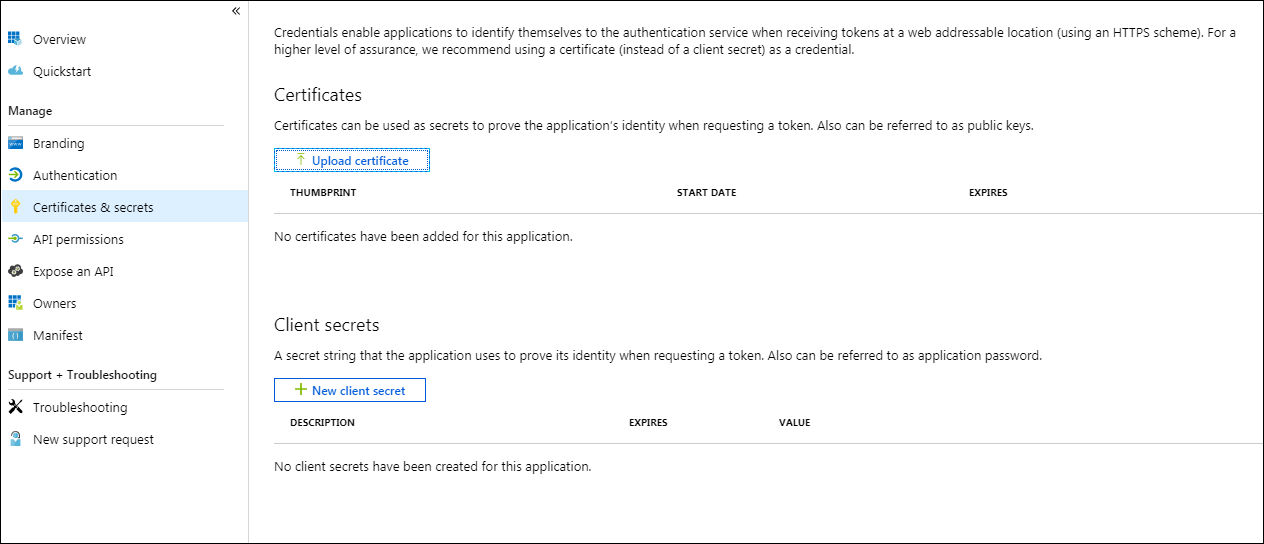
- ClickNew client secret
- SpecifyDescription(for example, Contract Express MSGraphClientSecret)
- SelectExpiresoption(we strongly do not recommend set as Never)
- ClickAdd
- Take a note ofValueas this is the value ofand it will be not possible to display that againMSGraphClientSecret
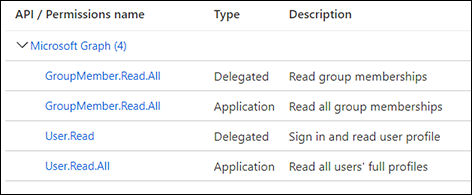
- SelectAPI permissionsblade within the created application.
- ClickAdd a permission.
- In a pop-up blade, selectMicrosoft Graph
- ClickDelegate permissionsand select the following:
- GroupMember.Read.All
- User.Read
- Click Application permissions and select the following:
- GroupMember.Read.All
- User.Read.All
- ClickAdd permissions
- You should see all added API/permissions
- SelectAuthenticationblade within created application:
- UnderRedirect URIs, add the Contract Express%The_UI_URL%/admin/authenticationendpoint as a new Web type entry (for example, https://contoso.contractexpress.com/app/admin/authentication)
- UnderAdvanced settings, check-inAccess tokensandID tokens
- ClickSave
Contract Express – Back-end Configuration
- Update value ofMSGraphClientIdparameter with previously capturedMSGraphClientId
- Update value ofMSGraphClientSecretparameter with previously capturedMSGraphClientSecret
- Update value ofMSGraphClientIdparameter with previously capturedMSGraphClientId
- Update value ofMSGraphClientSecretparameter with previously capturedMSGraphClientSecret
- Update value ofMSGraphTenantparameter with previously capturedMSGraphTenantnoteIf "Supported account type" is selected as "Accounts in any organizational director" during the application provisioning, you may want to use Common asMSGraphTenantvalue.
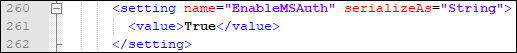
- Update value ofEnableMSAuthparameter withTrue.
Contract Express – Front-end Configuration
- Loginas Admin user to Contract Express.
- Navigate toAdminpage.
- SelectAuthenticationunder Licence(this option is visible only if CE SSO with Microsoft Entra ID is configured)
- Click onhere.
- Onceredirectedto Azure Portal, use the Microsoft Entra ID Global Admin credentials to authenticate.
- On the next screen clickAccept(this will establish trust between Contract Express and Azure)
- Once accepted, the page will redirect to the Contract Express application.
This article applies to:
- Product: Contract Express
